![Important] [Setup Manual available] E-Journal and Database Authentication System will Change — Kyoto University Katsura Library | Engineering Libraries Important] [Setup Manual available] E-Journal and Database Authentication System will Change — Kyoto University Katsura Library | Engineering Libraries](https://www.kulib.kyoto-u.ac.jp/uploads/new_authentication_image_eng.png)
Important] [Setup Manual available] E-Journal and Database Authentication System will Change — Kyoto University Katsura Library | Engineering Libraries

Unlocking the Secrets of Django's Authentication System: An Extensive Exploration | by elijah samson | AWS Tip

Learn the Django User Authentication System | by Dane Hillard | Kite — The Smart Programming Tool for Python | Medium
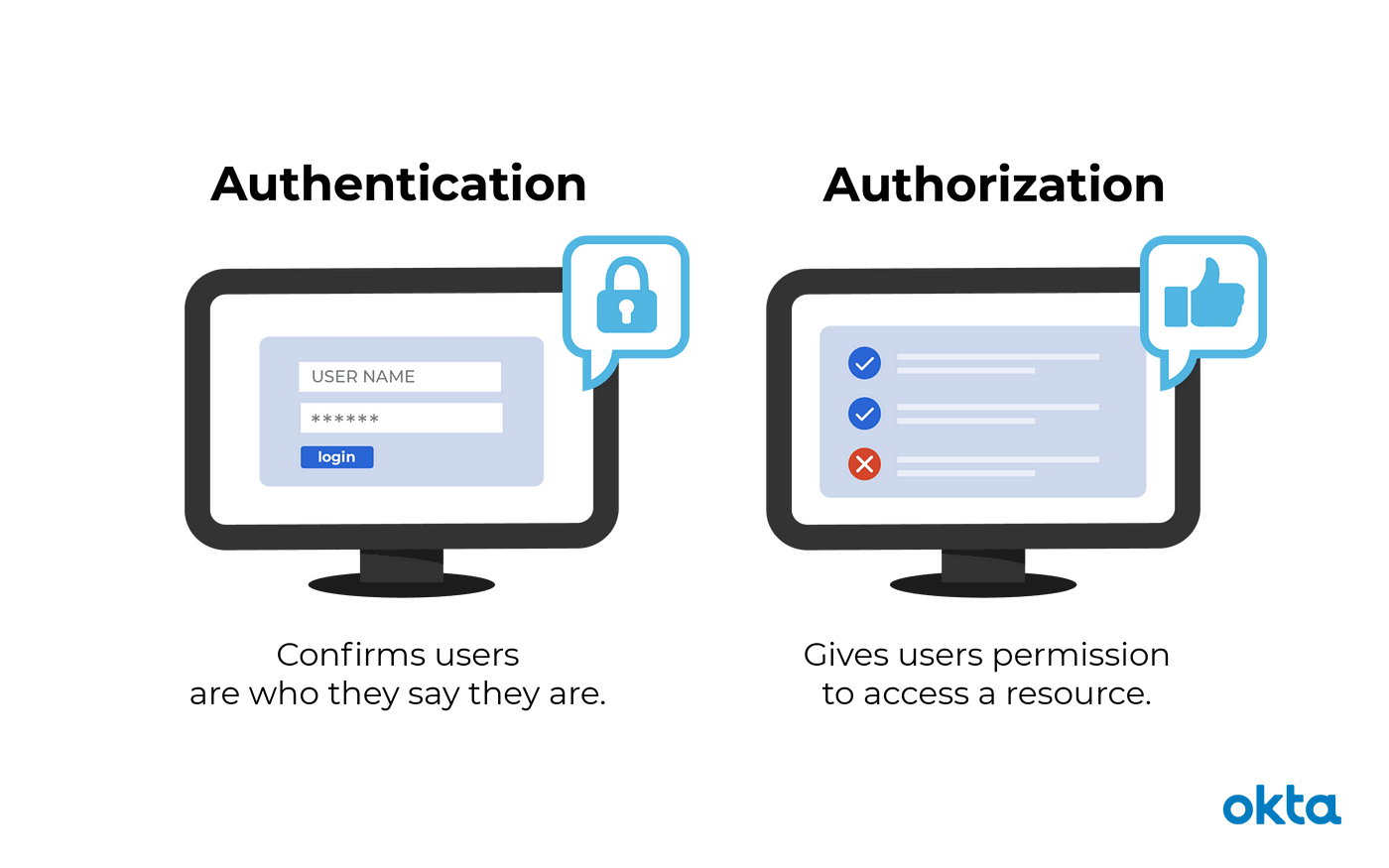
Authentication and Authorization. Visit systemdesign.us for System Design… | by PB | SystemDesign.us Blog | Medium
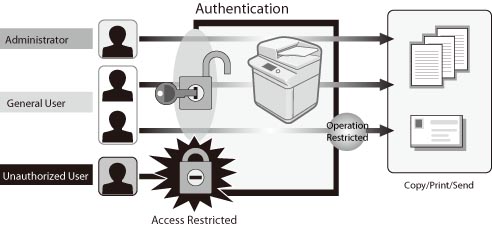
Overview of the Authentication System - Canon - imageRUNNER ADVANCE C3330i C3325i C3320 C3320i - User's Guide (Product Manual)

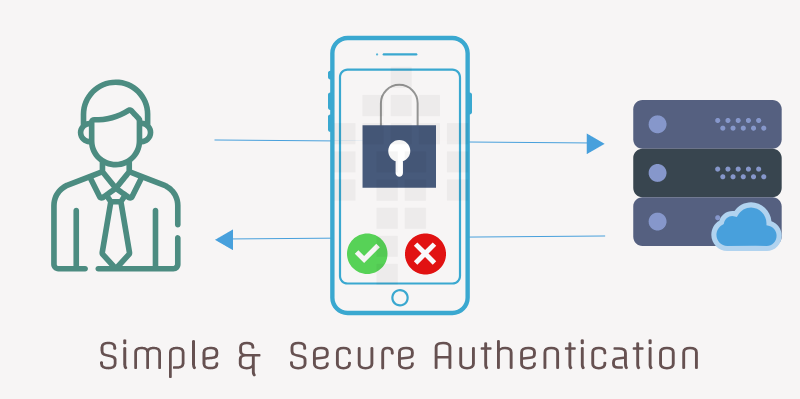
Authentication System Ppt Powerpoint Presentation Infographic Examples Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates







:max_bytes(150000):strip_icc()/twofactor-authentication-2fa.asp-final-5dc205d2a08b447abfb2e15eb131e28e.png)
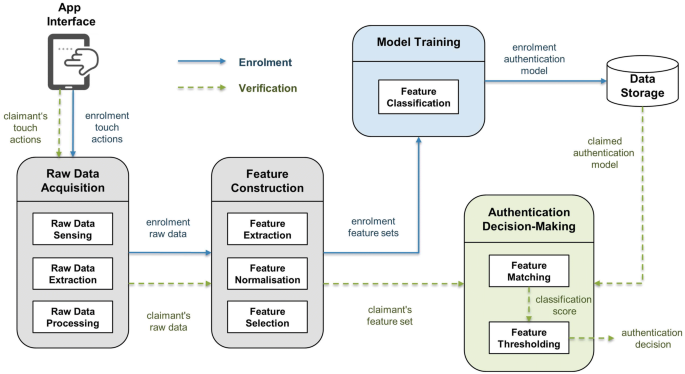
![PDF] Proposal: a design of e-learning user authentication system | Semantic Scholar PDF] Proposal: a design of e-learning user authentication system | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/62935229a5b3666237f963ba8656048c35c7a090/2-Figure1-1.png)
![SYSTEM DESIGN] authentication microservice for multiple backend microservices - Blind SYSTEM DESIGN] authentication microservice for multiple backend microservices - Blind](https://d2u3dcdbebyaiu.cloudfront.net/uploads/atch_img/60/5df5da438697b629d7a3330f61fe45f1_res.png)