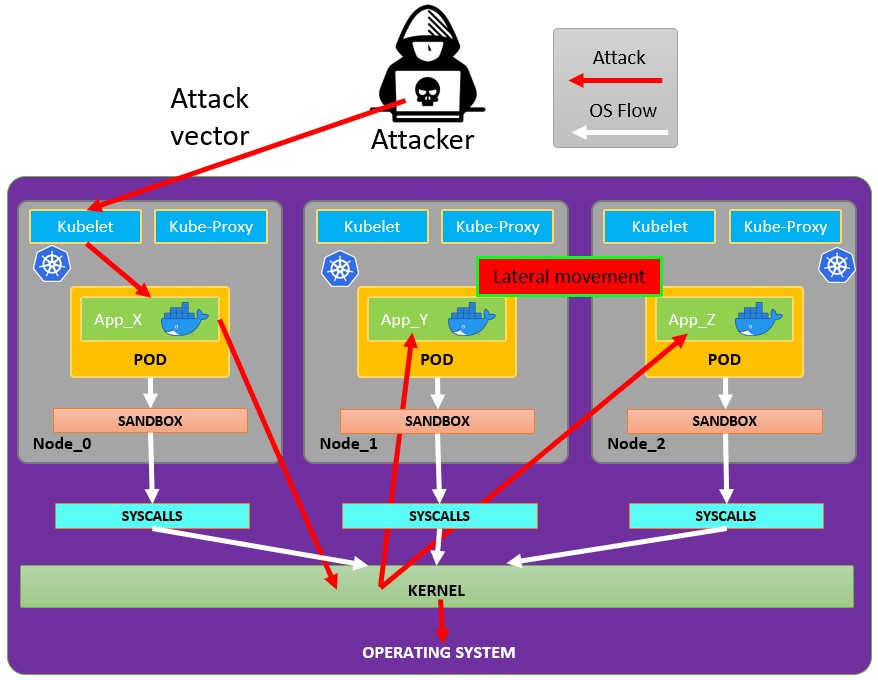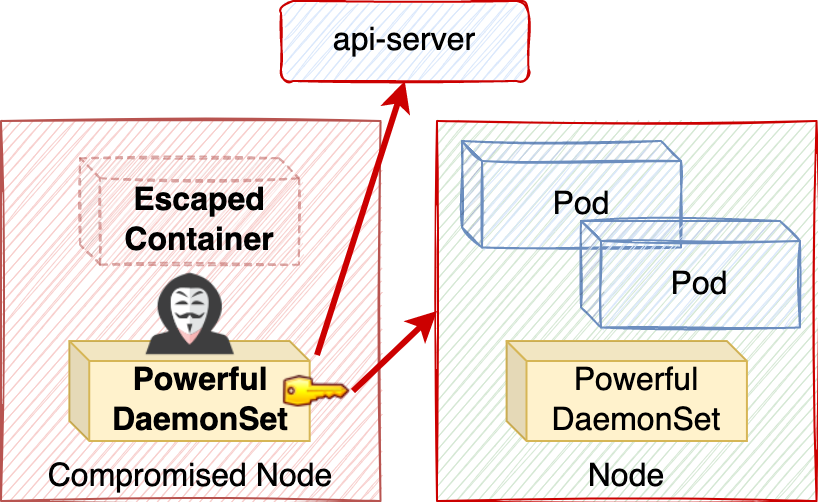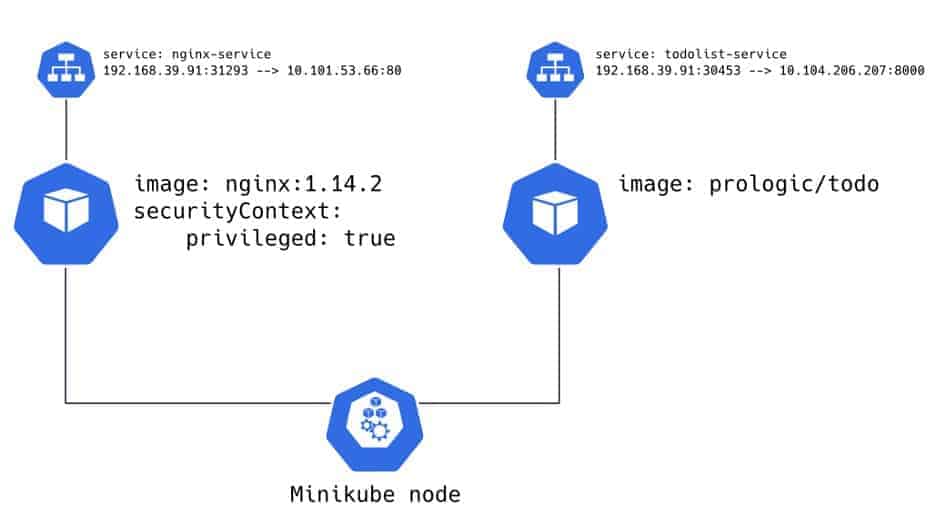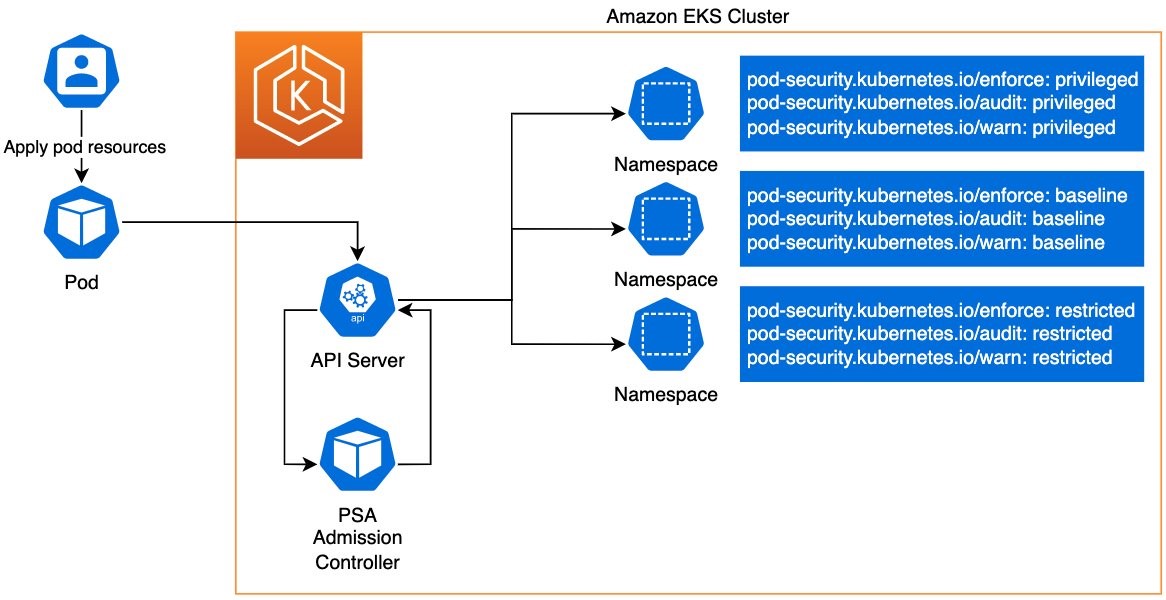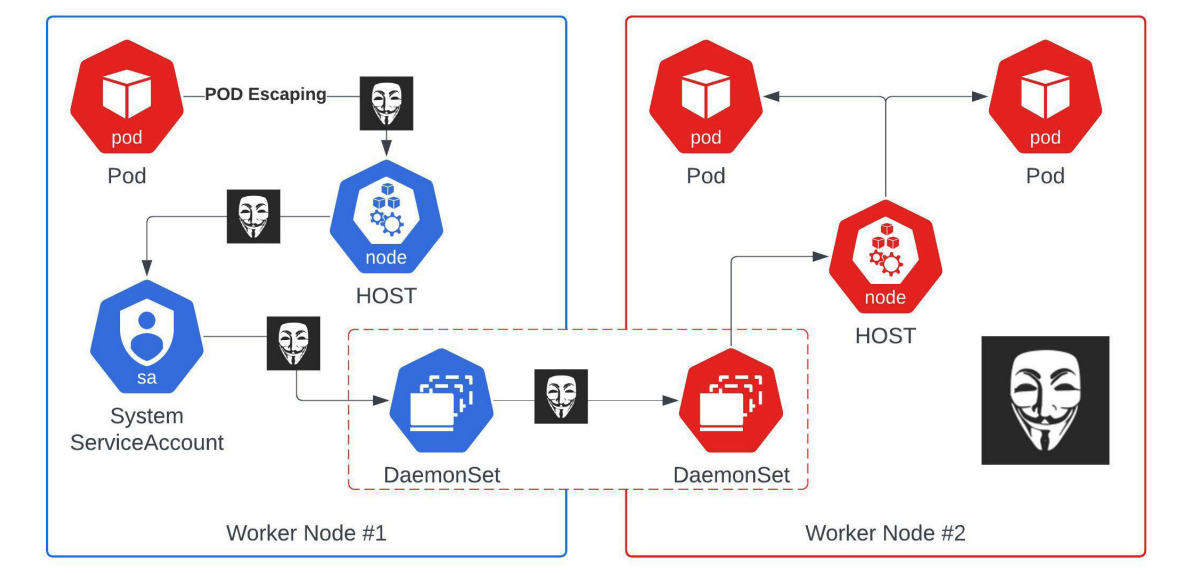
From dev to admin: an easy Kubernetes privilege escalation you should be aware of — the defense | by Federico Carbonetti | FAUN — Developer Community 🐾
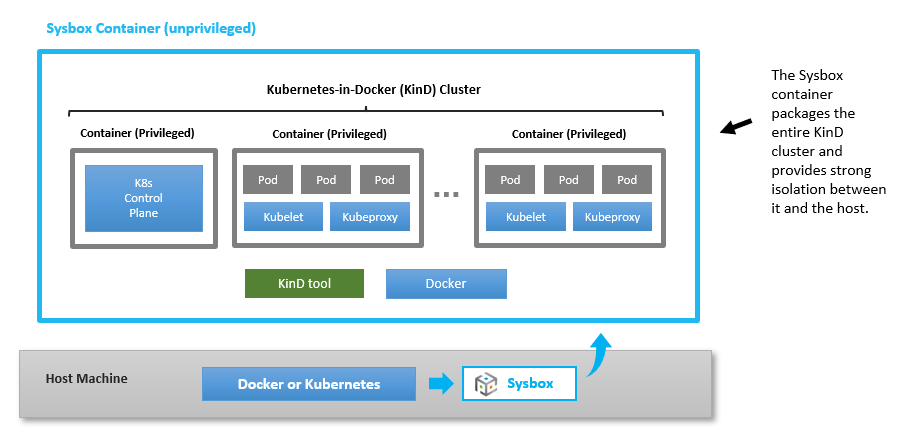
GitHub - kubewarden/pod-privileged-policy: A Kubewarden Policy that limits the ability to create privileged containers